您好,登錄后才能下訂單哦!
您好,登錄后才能下訂單哦!
這篇文章給大家介紹Burpsuite插件burpFakeIP怎么用,內容非常詳細,感興趣的小伙伴們可以參考借鑒,希望對大家能有所幫助。
今天給大家介紹一款Burpsuite插件,burpFakeIP
一、下載地址
https://github.com/TheKingOfDuck/burpFakeIP
二、安裝插件
1、解壓到本地
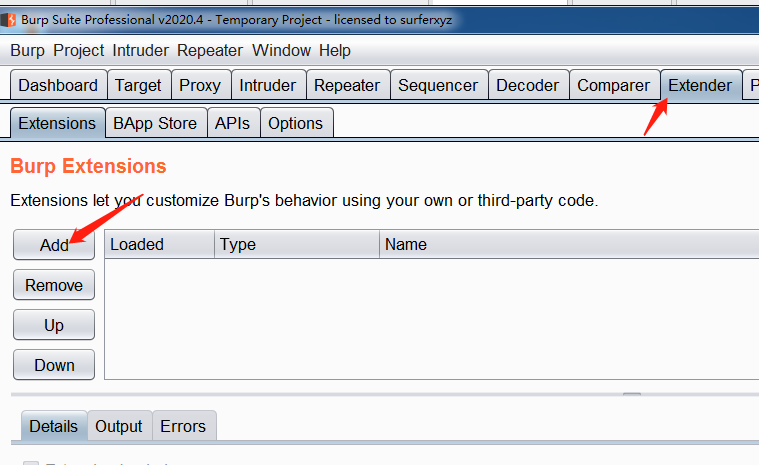
2、打開burpsuite,選擇Extender,Add
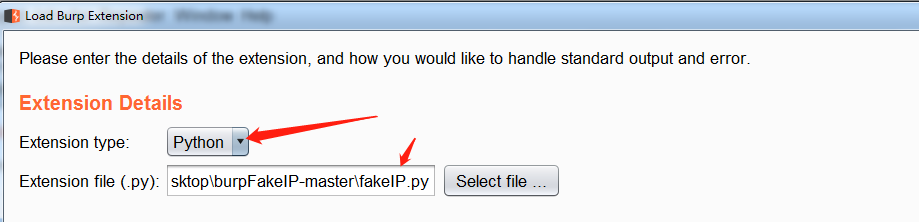
3、選擇下載好python插件,選擇下一步
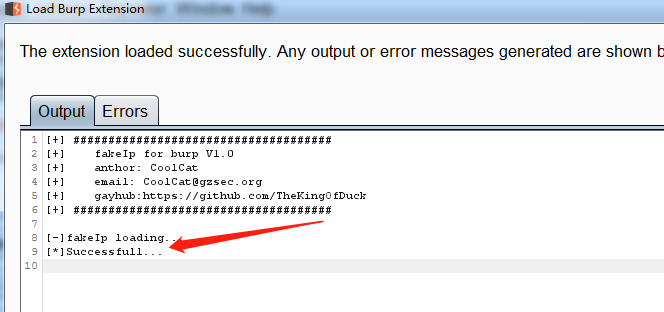
4、安裝成功
三、使用方法
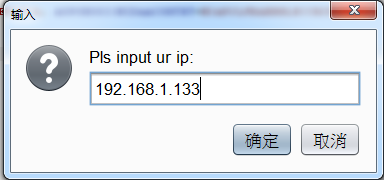
1、偽造指定ip,右擊抓到的數據包,選擇fakeip,inputIP,輸入想要用的ip地址,點擊確定,自動添加
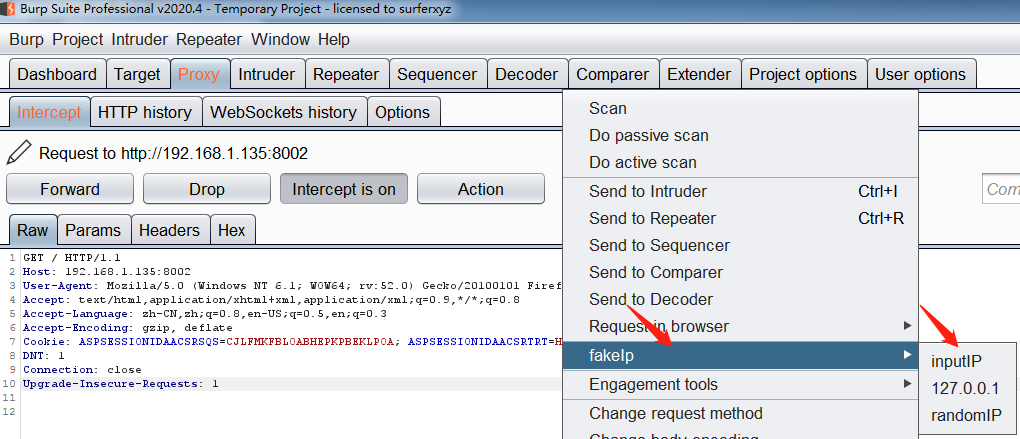
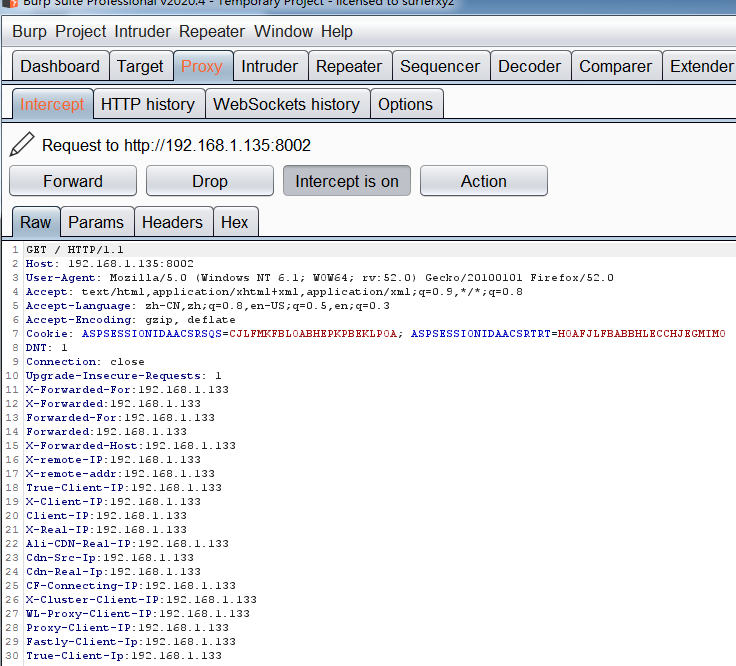
2、偽造本地ip,右擊數據包選擇127.0.0.1,自動生成如下數據包
GET / HTTP/1.1Host: 192.168.1.135:8002User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:52.0) Gecko/20100101 Firefox/52.0Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3Accept-Encoding: gzip, deflateCookie: ASPSESSIONIDAACSRSQS=CJLFMKFBLOABHEPKPBEKLPOA; ASPSESSIONIDAACSRTRT=HOAFJLFBABBHLECCHJEGMIMODNT: 1Connection: closeUpgrade-Insecure-Requests: 1X-Forwarded-For:127.0.0.1X-Forwarded:127.0.0.1Forwarded-For:127.0.0.1Forwarded:127.0.0.1X-Forwarded-Host:127.0.0.1X-remote-IP:127.0.0.1X-remote-addr:127.0.0.1True-Client-IP:127.0.0.1X-Client-IP:127.0.0.1Client-IP:127.0.0.1X-Real-IP:127.0.0.1Ali-CDN-Real-IP:127.0.0.1Cdn-Src-Ip:127.0.0.1Cdn-Real-Ip:127.0.0.1CF-Connecting-IP:127.0.0.1X-Cluster-Client-IP:127.0.0.1WL-Proxy-Client-IP:127.0.0.1Proxy-Client-IP:127.0.0.1Fastly-Client-Ip:127.0.0.1True-Client-Ip:127.0.0.1
3、偽造隨機IP,右擊數據包選擇randomIP,生成如下數據包
GET / HTTP/1.1Host: 192.168.1.135:8002User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:52.0) Gecko/20100101 Firefox/52.0Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3Accept-Encoding: gzip, deflateCookie: ASPSESSIONIDAACSRSQS=CJLFMKFBLOABHEPKPBEKLPOA; ASPSESSIONIDAACSRTRT=HOAFJLFBABBHLECCHJEGMIMODNT: 1Connection: closeUpgrade-Insecure-Requests: 1X-Forwarded-For:37.120.247.234X-Forwarded:37.120.247.234Forwarded-For:37.120.247.234Forwarded:37.120.247.234X-Forwarded-Host:37.120.247.234X-remote-IP:37.120.247.234X-remote-addr:37.120.247.234True-Client-IP:37.120.247.234X-Client-IP:37.120.247.234Client-IP:37.120.247.234X-Real-IP:37.120.247.234Ali-CDN-Real-IP:37.120.247.234Cdn-Src-Ip:37.120.247.234Cdn-Real-Ip:37.120.247.234CF-Connecting-IP:37.120.247.234X-Cluster-Client-IP:37.120.247.234WL-Proxy-Client-IP:37.120.247.234Proxy-Client-IP:37.120.247.234Fastly-Client-Ip:37.120.247.234True-Client-Ip:37.120.247.234
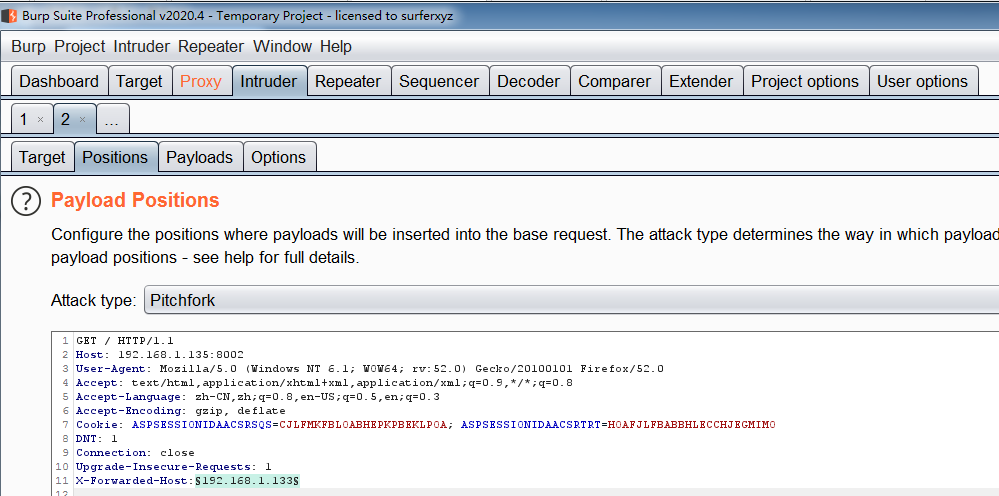
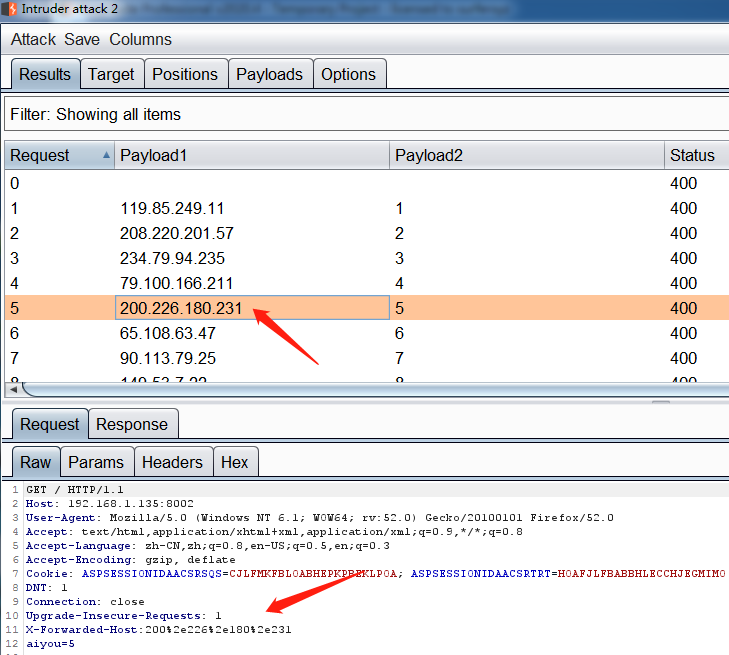
4、隨機ip爆破,偽造隨機ip爆破是本插件最核心的功能。
將數據包發送到Intruder模塊,在Positions中切換Attack type為Pitchfork模式,選擇好有效的偽造字段,以及需要爆破的字段
將Payload來源設置為Extensin-generated,并設置負載偽fakeIpPayloads,然后設置第二個變量。
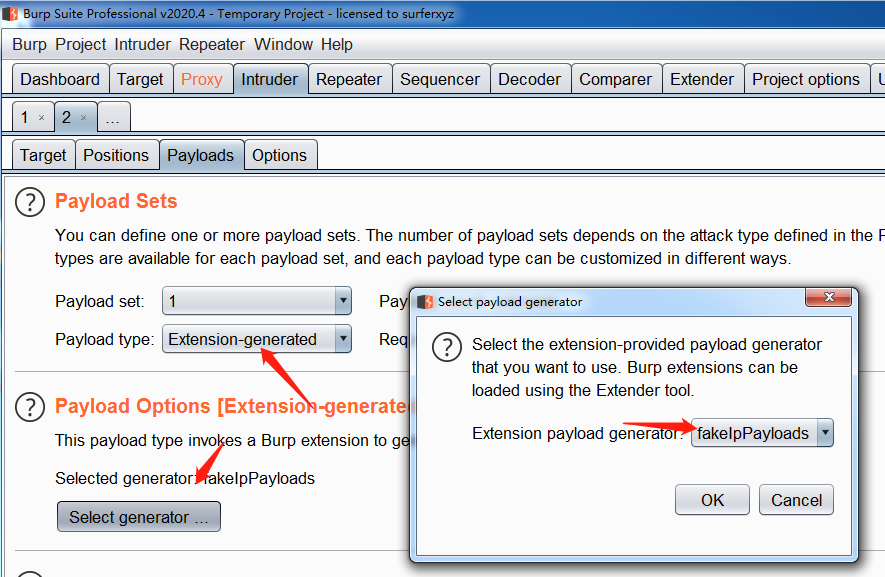
點擊Start attack開始爆破.
關于Burpsuite插件burpFakeIP怎么用就分享到這里了,希望以上內容可以對大家有一定的幫助,可以學到更多知識。如果覺得文章不錯,可以把它分享出去讓更多的人看到。
免責聲明:本站發布的內容(圖片、視頻和文字)以原創、轉載和分享為主,文章觀點不代表本網站立場,如果涉及侵權請聯系站長郵箱:is@yisu.com進行舉報,并提供相關證據,一經查實,將立刻刪除涉嫌侵權內容。