您好,登錄后才能下訂單哦!
您好,登錄后才能下訂單哦!
USG防火墻中的NAT配置,很多新手對此不是很清楚,為了幫助大家解決這個難題,下面小編將為大家詳細講解,有這方面需求的人可以來學習下,希望你能有所收獲。
USG防火墻 NAT配置
學習目的
掌握在USG防火墻上配置NATServer的方法
掌握在USG防火墻上配置NATEasy IP的方法
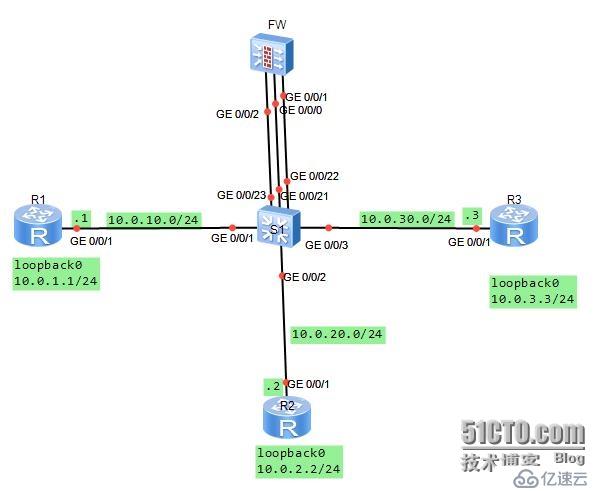
拓撲圖
場景:
你是公司的網絡管理員。公司使用網絡防火墻隔離成三個區域。現在要將DMZ區域中的一臺服務器(IP地址:10.0.3.3)提供的telnet服務發布出去,對外公開的地址是10.0.10.20、24.并且內部網絡Trust區域的用戶通過Easy-IP的方式訪問外部區域。其它方向的訪問被禁止。
在交換機上將G0/0/1與G0/0/21接口定義到vlan11,將G0/0/2與G0/0/22接口定義到vlan12,將G0/0/3與G0/0/23接口定義到vlan13.分別規劃了三個網段。
學習任務
步驟一.基本配置與IP編址
首先給三個路由器配置地址信息。
[Huawei]sysname R1
[R1]interface g0/0/1
[R1-GigabitEthernet0/0/1]ip add 10.0.10.124
[R1-GigabitEthernet0/0/1]desc this portconnect to S1-G0/0/1
[R1-GigabitEthernet0/0/1]interfaceloopback0
[R1-LoopBack0]ip add 10.0.1.1 24
[R1-LoopBack0]q
[Huawei]sysname R2
[R2]interface g0/0/1
[R2-GigabitEthernet0/0/1]ip add 10.0.20.224
[R2-GigabitEthernet0/0/1]desc this portconnect to S1-G0/0/2
[R2-GigabitEthernet0/0/1]interfaceloopback0
[R2-LoopBack0]ip add 10.0.2.2 24
[R2-LoopBack0]q
[Huawei]sysname R3
[R3]interface g0/0/1
[R3-GigabitEthernet0/0/1]ip add 10.0.30.324
[R3-GigabitEthernet0/0/1]desc this portconnect to S1-G0/0/3
[R3-GigabitEthernet0/0/1]interfaceloopback0
[R3-LoopBack0]ip add 10.0.3.3 24
[R3-LoopBack0]q
給防火墻配置地址時,G0/0/1配置10.0.20.254/24.
[SRG]sysname FW
13:06:03 2014/07/08
[FW]interface g0/0/1
13:06:30 2014/07/08
[FW-GigabitEthernet0/0/1]ip add 10.0.20.25424
13:07:01 2014/07/08
[FW-GigabitEthernet0/0/1]desc this portconnect to S1-G0/0/22
13:07:52 2014/07/08
[FW-GigabitEthernet0/0/1]interface g0/0/0
13:08:23 2014/07/08
[FW-GigabitEthernet0/0/0]dis this
13:08:31 2014/07/08
#
interface GigabitEthernet0/0/0
alias GE0/MGMT
ipaddress 192.168.0.1 255.255.255.0
dhcpselect interface
dhcpserver gateway-list 192.168.0.1
#
return
[FW-GigabitEthernet0/0/0]undo ip add
13:08:42 2014/07/08
Info: The DHCP server configuration on thisinterface will be deleted.
[FW-GigabitEthernet0/0/0]display this
13:08:46 2014/07/08
#
interface GigabitEthernet0/0/0
alias GE0/MGMT
#
return
[FW-GigabitEthernet0/0/0]ip add 10.0.10.25424
13:09:29 2014/07/08
[FW-GigabitEthernet0/0/0]desc this portconnect to S1-G0/0/21
13:10:05 2014/07/08
[FW-GigabitEthernet0/0/0]interface G0/0/2
13:10:15 2014/07/08
[FW-GigabitEthernet0/0/2]ip add 10.0.30.25424
13:10:28 2014/07/08
[FW-GigabitEthernet0/0/2]desc this portconnect to S1-G0/0/23
13:10:53 2014/07/08
[FW-GigabitEthernet0/0/2]q
交換機上需要按照需求定義vlan
[Huawei]sysname S1
[S1]vlan batch 11 to 13
Info: This operation may take a fewseconds. Please wait for a moment...done.
[S1]interface g0/0/1
[S1-GigabitEthernet0/0/1]port link-typeaccess
[S1-GigabitEthernet0/0/1]port default vlan11
[S1]interface g0/0/2
[S1-GigabitEthernet0/0/2]port link-typeaccess
[S1-GigabitEthernet0/0/2]port default vlan12
[S1-GigabitEthernet0/0/2]interface g0/0/3
[S1-GigabitEthernet0/0/3]port link-typeaccess
[S1-GigabitEthernet0/0/3]port default vlan13
[S1-GigabitEthernet0/0/3]interface g0/0/21
[S1-GigabitEthernet0/0/21]port link-typeaccess
[S1-GigabitEthernet0/0/21]port default vlan11
[S1-GigabitEthernet0/0/21]interface g0/0/22
[S1-GigabitEthernet0/0/22]port link-typeaccess
[S1-GigabitEthernet0/0/22]port default vlan12
[S1-GigabitEthernet0/0/22]interface g0/0/23
[S1-GigabitEthernet0/0/23]port link-typeaccess
[S1-GigabitEthernet0/0/23]port default vlan13
步驟二.將接口配置到安全區域
防火墻默認有四個區域,分別是“local”、“trust"、“untrust”、“dmz”。
實驗中我們用到“trust”、'untrust"、“dmz”三個區域。將G0/0/0加入untrust區域、g/0/0/2加入dmz和g/0/0/1加入trust。
[FW]firewall zone trust
13:45:31 2014/07/08
[FW-zone-trust]dis this
13:45:35 2014/07/08
#
firewall zone trust
setpriority 85
addinterface GigabitEthernet0/0/0
#
return
[FW-zone-trust]undo add inter
[FW-zone-trust]undo add interface g0/0/0
13:46:01 2014/07/08
[FW-zone-trust]add interface g0/0/1
13:46:22 2014/07/08
[FW-zone-trust]firewall zone untrust
[FW-zone-untrust]add interface g0/0/0
13:47:24 2014/07/08
[[FW-zone-untrust]firewall zone dmz
13:48:06 2014/07/08
[FW-zone-dmz]add interface g0/0/2
13:48:13 2014/07/08
[FW-zone-dmz]q
默認情況下,防火墻并不允許出local區域外的其它區域之間進行通信。為了便于驗證配置的正確性,我們首先將防火墻區域之間的默認過濾規則配置為允許所有區域間通信。配置完成后在FW設備上測試連通性。
[FW]firewall packet-filter default permitall
13:51:19 2014/07/08
Warning:Setting the default packetfiltering to permit poses security risks. You
are advised to configure the securitypolicy based on the actual data flows. Are
you sure you want to continue?[Y/N]y
[FW]ping -c 1 10.0.10.1
13:51:56 2014/07/08
PING 10.0.10.1: 56 data bytes,press CTRL_C to break
Reply from 10.0.10.1: bytes=56 Sequence=1 ttl=255 time=90 ms
---10.0.10.1 ping statistics ---
1packet(s) transmitted
1packet(s) received
0.00% packet loss
round-trip min/avg/max = 90/90/90 ms
[FW]ping -c 1 10.0.20.2
13:52:08 2014/07/08
PING 10.0.20.2: 56 data bytes,press CTRL_C to break
Reply from 10.0.20.2: bytes=56 Sequence=1 ttl=255 time=400 ms
---10.0.20.2 ping statistics ---
1packet(s) transmitted
1packet(s) received
0.00% packet loss
round-trip min/avg/max = 400/400/400 ms
[FW]ping -c 1 10.0.30.3
13:52:18 2014/07/08
PING 10.0.30.3: 56 data bytes,press CTRL_C to break
Reply from 10.0.30.3: bytes=56 Sequence=1 ttl=255 time=410 ms
---10.0.30.3 ping statistics ---
1packet(s) transmitted
1packet(s) received
0.00% packet loss
round-trip min/avg/max = 410/410/410 ms
步驟三.配置靜態路由,實現網絡的連通性
在R2和R3上配置缺省路由,在FW上配置明確的靜態路由,實現三個loopback0接口之間的通信。R1無需定義缺省路由,原因是其作為internet設備,他不需要知道內部和DMZ區域的私有網絡信息。
[R2]ip route-static 0.0.0.0 0 10.0.20.254
[R3]ip route-static 0.0.0.0 0 10.0.30.254
[FW]ip route-static 10.0.1.0 24 10.0.10.1
13:58:26 2014/07/08
[FW]ip route-static 10.0.2.0 24 10.0.20.2
13:58:40 2014/07/08
[FW]ip route-static 10.0.3.0 24 10.0.30.3
13:58:52 2014/07/08
在防火墻上測試與10.0.1.0、10.0.2.0、10.0.3.0之間的連通性。
[FW]ping -c 1 10.0.1.1
14:00:18 2014/07/08
PING 10.0.1.1: 56 data bytes,press CTRL_C to break
Reply from 10.0.1.1: bytes=56 Sequence=1 ttl=255 time=80 ms
---10.0.1.1 ping statistics ---
1packet(s) transmitted
1packet(s) received
0.00% packet loss
round-trip min/avg/max = 80/80/80 ms
[FW]ping -c 1 10.0.2.2
14:00:25 2014/07/08
PING 10.0.2.2: 56 data bytes,press CTRL_C to break
Reply from 10.0.2.2: bytes=56 Sequence=1 ttl=255 time=170 ms
---10.0.2.2 ping statistics ---
1packet(s) transmitted
1packet(s) received
0.00% packet loss
round-trip min/avg/max = 170/170/170 ms
[FW]ping -c 1 10.0.3.3
14:00:29 2014/07/08
PING 10.0.3.3: 56 data bytes,press CTRL_C to break
Reply from 10.0.3.3: bytes=56 Sequence=1 ttl=255 time=110 ms
---10.0.3.3 ping statistics ---
1packet(s) transmitted
1packet(s) received
0.00% packet loss
round-trip min/avg/max = 110/110/110 ms
目前配置下,所有區域之間可以通訊,不被檢查。但是由于當前尚未定義NAT,外部區域不能與內部和DMZ區域相互訪問。
步驟四.配置區域間的安全過濾
配置從Trust區域的部分網段10.0.2.3發往Untrust區域的數據包被放行。從Untrust區域發往DMZ目標服務器10.0.3.3的telnet請求被放行。
[FW]firewall session link-state check
[FW]policy interzone trust untrust outbound
[FW-policy-interzone-trust-untrust-outbound]policy0
14:06:57 2014/07/08
[FW-policy-interzone-trust-untrust-outbound-0]policysource 10.0.2.0 0.0.0.255
14:07:18 2014/07/08
[FW-policy-interzone-trust-untrust-outbound-0]actionpermit
14:07:31 2014/07/08
[FW-policy-interzone-trust-untrust-outbound-0]q
14:07:40 2014/07/08
[FW-policy-interzone-trust-untrust-outbound]q
14:07:40 2014/07/08
]policy interzone dmz untrust inbound
14:09:01 2014/07/08
[FW-policy-interzone-dmz-untrust-inbound]policy0
14:09:08 2014/07/08
[FW-policy-interzone-dmz-untrust-inbound-0]policydestination 10.0.3.3 0
14:09:37 2014/07/08
[FW-policy-interzone-dmz-untrust-inbound-0]policyservice service-set telnet
[FW-policy-interzone-dmz-untrust-inbound-0]actionpermit
14:09:55 2014/07/08
[FW-policy-interzone-dmz-untrust-inbound-0]q
14:09:55 2014/07/08
步驟五.配置Easy-Ip,實現Trust區域到Untrust區域的訪問。
配置使用Easy-IP,進行NAT源地址轉換。并且將NAT與接口進行綁定。
[FW-nat-policy-interzone-trust-untrust-outbound]policy0
14:14:00 2014/07/08
[FW-nat-policy-interzone-trust-untrust-outbound-0]policysource 10.0.2.0 0.0.0.2
55
14:14:26 2014/07/08
[FW-nat-policy-interzone-trust-untrust-outbound-0]actionsource-nat
14:14:37 2014/07/08
[FW-nat-policy-interzone-trust-untrust-outbound-0]easy-ipg0/0/0
14:14:51 2014/07/08
[FW-nat-policy-interzone-trust-untrust-outbound-0]q
配置完成后,驗證Trust區域與Untrust區域之間的訪問是否正常。
<R2>ping 10.0.1.1
PING 10.0.1.1: 56 data bytes,press CTRL_C to break
Request time out
Request time out
Request time out
Request time out
Request time out
---10.0.1.1 ping statistics ---
5packet(s) transmitted
0packet(s) received
100.00% packet loss
<R2>ping -a 10.0.2.2 10.0.1.1
PING 10.0.1.1: 56 data bytes,press CTRL_C to break
Reply from 10.0.1.1: bytes=56 Sequence=1 ttl=254 time=220 ms
Reply from 10.0.1.1: bytes=56 Sequence=2 ttl=254 time=100 ms
Reply from 10.0.1.1: bytes=56 Sequence=3 ttl=254 time=100 ms
Reply from 10.0.1.1: bytes=56 Sequence=4 ttl=254 time=120 ms
Reply from 10.0.1.1: bytes=56 Sequence=5 ttl=254 time=440 ms
---10.0.1.1 ping statistics ---
5packet(s) transmitted
5packet(s) received
0.00% packet loss
round-trip min/avg/max = 100/196/440 ms
注意,這里直接測試與10.0.1.1之間的連通性,顯示不通。使用擴展ping,指定了發送數據包的源地址是10.0.2.2后,實現了連通性。原因是,直接發送數據包到10.0.1.1時,數據包的源地址到10.0.1.1時,數據包的源地址為10.0.20.2,該地址不屬于NAT轉換的客戶端地址范圍。
步驟六.將內網服務器10.0.3.3發布出去
配置內網服務器10.0.3.3的telnet服務,映射到地址10.0.10.20
[FW]nat server protocol tcp global10.0.10.20 telnet inside 10.0.3.3 telnet
在R3上開啟Telnet功能,并在R1上測試,測試時需要注意,對外發布的地址為10.0.10.20,所以R1對10.0.3.3訪問時,訪問的目標地址為10.0.10.20。
[R3]user-interface vty 0 4
[R3-ui-vty0-4]authentication-mode password
Please configure the login password(maximum length 16):16
[R3-ui-vty0-4]set authentication password ?
cipher Set the password withcipher text
[R3-ui-vty0-4]set authentication passwordcip
[R3-ui-vty0-4]set authentication passwordcipher Huawei
[R3-ui-vty0-4]user privilege level 3
[R3-ui-vty0-4]q
<R1>telnet 10.0.10.20
Press CTRL_] to quit telnet mode
Trying 10.0.10.20 ...
Connected to 10.0.10.20 ...
Login authentication
Password:
<R3>
看完上述內容是否對您有幫助呢?如果還想對相關知識有進一步的了解或閱讀更多相關文章,請關注億速云行業資訊頻道,感謝您對億速云的支持。
免責聲明:本站發布的內容(圖片、視頻和文字)以原創、轉載和分享為主,文章觀點不代表本網站立場,如果涉及侵權請聯系站長郵箱:is@yisu.com進行舉報,并提供相關證據,一經查實,將立刻刪除涉嫌侵權內容。