您好,登錄后才能下訂單哦!
您好,登錄后才能下訂單哦!
當mysql跨越互聯網進行復制時別人可以竊取到mysql的復制信息,這些信息是明文的,因此存在不安全性,這里通過ssl對復制的信息進行加密。
準備環境:
1.系統環境:Centos6.5
2.數據庫版本:5.5.36-MariaDB-log MariaDB Server
3.Host:
Master主機: master.samlee.com 172.16.100.7
Slave主機: slave.samlee.com 172.16.100.8
Public主機: public.samlee.com 172.16.100.9
----------------------------------------------------------------------------------------------------------
實現過程如下:
Public主機上操作:
1.創建證書中心:
--在public主機上創建證書中心 # cd /etc/pki/CA/ --生成私鑰 # (umask 077;openssl genrsa -out /etc/pki/CA/private/cakey.pem 2048)
生成自簽證書,由于需要輸入大量用戶信息,因此編輯證書的配置文件,在私有的CA上創建證書要注意所有的用戶信息要和CA中的一致,從國家到部門都要相同,否則會造成證書無法使用。
--根據實驗要求修改配置文件如下: # vim /etc/pki/tls/openssl.cnf [ req_distinguished_name ] countryName_default = CN stateOrProvinceName_default = GUANGDONG localityName_default = GUANGZHOU 0.organizationName_default = JUST.LTD organizationalUnitName_default = IT
生成自簽證書--以CAserver的身份自建CA證書
# openssl req -new -x509 -key /etc/pki/CA/private/cakey.pem -out /etc/pki/CA/cacert.pem -days 3650 Country Name (2 letter code) [CN]: State or Province Name (full name) [GUANGDONG]: Locality Name (eg, city) [GUANGZHOU]: Organization Name (eg, company) [JUST.LTD]: Organizational Unit Name (eg, section) [IT]: Common Name (eg, your name or your server's hostname) []:public.samlee.com
創建證書編號
# touch {index.txt,serial}
# echo 01 > serial給Master服務器生成key、證書請求、證書:
--創建私鑰 # cd /etc/pki/CA/ # (umask 077;openssl genrsa -out master.key 2048) --生成證書申請 # openssl req -new -key master.key -out master.csr Country Name (2 letter code) [CN]: State or Province Name (full name) [GUANGDONG]: Locality Name (eg, city) [GUANGZHOU]: Organization Name (eg, company) [JUST.LTD]: Organizational Unit Name (eg, section) [IT]: Common Name (eg, your name or your server's hostname) []:master.samlee.com --在證書服務器上對master的證書進行簽發 # openssl ca -in master.csr -out master.crt -days 3650 Using configuration from /etc/pki/tls/openssl.cnf Check that the request matches the signature Signature ok Certificate Details: Serial Number: 1 (0x1) Validity Not Before: Jun 23 00:09:31 2016 GMT Not After : Jun 21 00:09:31 2026 GMT Subject: countryName = CN stateOrProvinceName = GUANGDONG organizationName = JUST.LTD organizationalUnitName = IT commonName = master.samlee.com Data Base Updated --看到此項出現說明證書簽發成功了
給Slave服務器生成key、證書請求、證書:
--創建私鑰 # cd /etc/pki/CA/ # (umask 077;openssl genrsa -out slave.key 2048) --生成證書申請 # openssl req -new -key slave.key -out slave.csr Country Name (2 letter code) [CN]: State or Province Name (full name) [GUANGDONG]: Locality Name (eg, city) [GUANGZHOU]: Organization Name (eg, company) [JUST.LTD]: Organizational Unit Name (eg, section) [IT]: Common Name (eg, your name or your server's hostname) []:slave.samlee.com --在證書服務器上對master的證書進行簽發 # openssl ca -in slave.csr -out slave.crt -days 3650 Using configuration from /etc/pki/tls/openssl.cnf Check that the request matches the signature Signature ok Certificate Details: Serial Number: 2 (0x2) Validity Not Before: Jun 23 00:18:21 2016 GMT Not After : Jun 21 00:18:21 2026 GMT Subject: countryName = CN stateOrProvinceName = GUANGDONG organizationName = JUST.LTD organizationalUnitName = IT commonName = slave.samlee.com Data Base Updated --看到此項出現說明證書簽發成功了
Master與Slavr主機上操作:
2.在Master主機和Slave主機上安裝MariaDB
使用軟件安裝包為mariadb-5.5.36-linux-x86_64.tar.gz,上傳至root目錄下,安裝配置Mairadb,并設置mydata目錄為數據和日志存放目錄;以下步驟在node1和node2上一致
# cd /root
# tar -xzf mariadb-5.5.36-linux-x86_64.tar.gz -C /usr/local/
# ln -sv mariadb-5.5.36-linux-x86_64 mysql
# groupadd=mysql
# useradd=mysql -g mysql
# mkdir /mydata/{data,binlog,relaylog} -pv
# chown -R mysql.mysql /mydata/*
# mkdir /etc/mysql
# cp /usr/local/mysql/support-files/my-large.cnf /etc/mysql/my.cnf
修改/etc/mysql/my.cnf
# vim /etc/mysql/my.cnf 最后一行增加以下語句
datadir=/mydata
# chown -R mysql.mysql /etc/mysql/*
# echo "export PATH=$PATH:/usr/local/mysql/bin" > /etc/profile.d/mysql.sh
# source /etc/profile.d/mysql.sh
# mkdir /var/lib/mysql/
# chown -R mysql.mysql /var/lib/mysql/
# cd /usr/local/mysql
# cp /usr/local/mysql/support-files/mysql.server /etc/init.d/mysqld
# chmod +x /etc/init.d/mysqld
# scripts/mysql_install_db --user=mysql --datadir=/mydata/data
# service mysqld restartMaster主機上操作:
3.配置Master主機為主節點(主服務器)
--創建二進制日志存儲目錄及目錄權限授予 # mkdir -pv /mydata/binglogs # chown -R mysql.mysql /mydata/binglogs --配置my.cnf設置Master為主節點 server-id = 1 log-bin=/mydata/binglogs/master-binlog
Slave主機上操作:
4.配置Slave主機為從節點(從服務器)
--創建中繼日志存儲目錄及目錄權限授予 # mkdir -pv /mydata/relaylogs # chown -R mysql.mysql /mydata/relaylogs --配置my.cnf設置Master為主節點 server-id = 11 relay-log=/mydata/relaylogs/relay-bin
Master主機上操作:
創建擁有復制權限的用戶
--在Master創建擁有復制權限的用戶,支持SSL認證,新建一個用戶repluser@'172.16.100.%',密碼replpass,并授權所有訪問權限 MariaDB [(none)]> GRANT REPLICATION SLAVE,REPLICATION CLIENT ON *.* TO 'repluser'@'172.16.%.%' IDENTIFIED BY 'replpass' REQUIRE ssl; MariaDB [(none)]> FLUSH PRIVILEGES; MariaDB [(none)]> SHOW MASTER STATUS; +----------------------+----------+--------------+------------------+ | File | Position | Binlog_Do_DB | Binlog_Ignore_DB | +----------------------+----------+--------------+------------------+ | master-binlog.000001 | 684 | | | +----------------------+----------+--------------+------------------+
5.配置Master主機與Slave主機支持SSL認證
Master主機上操作:
配置Master主機支持SSL認證:
--創建文件夾用于存放ca證書和Master自己的key+證書 # mkdir /etc/mysql/ssl --從Public主機獲取CA證書及自己的證書 # scp root@172.16.100.9:/etc/pki/CA/private/cakey.pem /etc/mysql/ssl/ # scp root@172.16.100.9:/etc/pki/CA/cacert.pem /etc/mysql/ssl/ # scp root@172.16.100.9:/etc/pki/CA/master.key /etc/mysql/ssl/ # scp root@172.16.100.9:/etc/pki/CA/master.crt /etc/mysql/ssl/ # chown -R mysql.mysql /etc/mysql/ssl --修改mysql的配置文件,使mysql支持ssl模式 # vim /etc/mysql/my.cnf ssl 開啟SSL功能 ssl-ca = /etc/mysql/ssl/cacert.pem 指定CA文件位置 ssl-cert = /etc/mysql/ssl/master.crt 指定證書文件位置 ssl-key = /etc/mysql/ssl/master.key 指定密鑰所在位置 --重啟mysql服務 # service mysqld restart --查詢SSL相關變量是否啟動 mysql > SHOW GLOBAL VARIABLES LIKE '%ssl%'; +---------------+---------------------------+ | Variable_name | Value | +---------------+---------------------------+ | have_openssl | YES | | have_ssl | YES | | ssl_ca | /etc/mysql/ssl/cakey.pem | | ssl_capath | | | ssl_cert | /etc/mysql/ssl/master.crt | | ssl_cipher | | | ssl_key | /etc/mysql/ssl/master.key | +---------------+---------------------------+
Slave主機上操作:
配置Slave主機支持SSL認證:
--創建文件夾用于存放ca證書和Master自己的key+證書 # mkdir /etc/mysql/ssl --從Public主機獲取CA證書及自己的證書 # scp root@172.16.100.9:/etc/pki/CA/private/cakey.pem /etc/mysql/ssl/ # scp root@172.16.100.9:/etc/pki/CA/cacert.pem /etc/mysql/ssl/ # scp root@172.16.100.9:/etc/pki/CA/slave.key /etc/mysql/ssl/ # scp root@172.16.100.9:/etc/pki/CA/slave.crt /etc/mysql/ssl/ # chown -R mysql.mysql /etc/mysql/ssl --修改mysql的配置文件,使mysql支持ssl模式 # vim /etc/mysql/my.cnf ssl 開啟SSL功能 ssl-ca = /etc/mysql/ssl/cacert.pem 指定CA文件位置 ssl-cert = /etc/mysql/ssl/slave.crt 指定證書文件位置 ssl-key = /etc/mysql/ssl/slave.key 指定密鑰所在位置 --重啟mysql服務 # service mysqld restart --查詢SSL相關變量是否啟動 mysql > SHOW VARIABLES LIKE '%ssl%'; +---------------+--------------------------+ | Variable_name | Value | +---------------+--------------------------+ | have_openssl | YES | | have_ssl | YES | | ssl_ca | /etc/mysql/ssl/cakey.pem | | ssl_capath | | | ssl_cert | /etc/mysql/ssl/slave.crt | | ssl_cipher | | | ssl_key | /etc/mysql/ssl/slave.key | +---------------+--------------------------+
6.Slave通過SSL遠程連接訪問Master主服務器
# mysql -urepluser -preplpass -h272.16.100.7 --ssl-ca=/etc/mysql/ssl/cacert.pem --ssl-cert=/etc/mysql/ssl/slave.crt --ssl-key=/etc/mysql/ssl/slave.key
7.Slave以ssl的方式連接數據庫,并設置支持主從復制默認
mysql > CHANGE MASTER TO MASTER_HOST='172.16.100.7',MASTER_USER='repluser',MASTER_PASSWORD='replpass',master_ssl=1,master_ssl_ca='/etc/mysql/ssl/cacert.pem',master_ssl_cert='/etc/mysql/ssl/slave.crt',master_ssl_key='/etc/mysql/ssl/slave.key',MASTER_LOG_FILE='master-binlog.000005',MASTER_LOG_POS=245; > SHOW SLAVE STATUS\G *************************** 1. row *************************** Slave_IO_State: Waiting for master to send event Master_Host: 172.16.100.7 Master_User: repluser Master_Port: 3306 Connect_Retry: 60 Master_Log_File: master-binlog.000005 Read_Master_Log_Pos: 245 Relay_Log_File: relay-bin.000002 Relay_Log_Pos: 533 Relay_Master_Log_File: master-binlog.000005 Slave_IO_Running: Yes Slave_SQL_Running: Yes Replicate_Do_DB: Replicate_Ignore_DB: Replicate_Do_Table: Replicate_Ignore_Table: Replicate_Wild_Do_Table: Replicate_Wild_Ignore_Table: Last_Errno: 0 Last_Error: Skip_Counter: 0 Exec_Master_Log_Pos: 245 Relay_Log_Space: 821 Until_Condition: None Until_Log_File: Until_Log_Pos: 0 Master_SSL_Allowed: Yes Master_SSL_CA_File: /etc/mysql/ssl/cacert.pem Master_SSL_CA_Path: Master_SSL_Cert: /etc/mysql/ssl/slave.crt Master_SSL_Cipher: Master_SSL_Key: /etc/mysql/ssl/slave.key Seconds_Behind_Master: 0 Master_SSL_Verify_Server_Cert: No Last_IO_Errno: 0 Last_IO_Error: Last_SQL_Errno: 0 Last_SQL_Error: Replicate_Ignore_Server_Ids: Master_Server_Id: 1
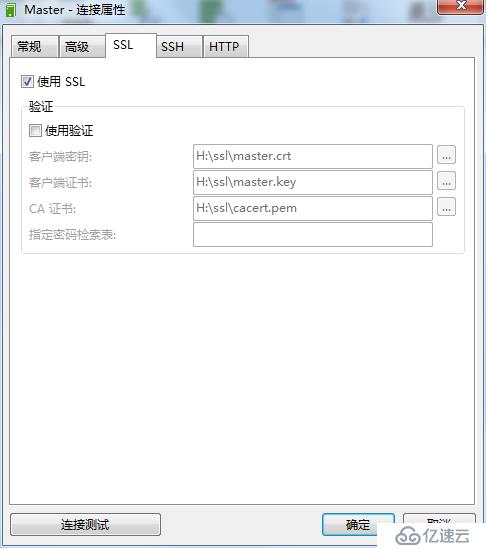
8.Windows下通過“Navicat for MySQL”以ssl的方式連接訪問數據庫Master主節點服務器
將node1/etc/mysql/ssl下的幾個文件存放到windows上,此處我放到我的H盤下ssl目錄
注意,在ssl里選擇證書和key的時候,需要先點擊“使用驗證”,等選擇完畢后再勾除“使用驗證”
配置如下所示:

免責聲明:本站發布的內容(圖片、視頻和文字)以原創、轉載和分享為主,文章觀點不代表本網站立場,如果涉及侵權請聯系站長郵箱:is@yisu.com進行舉報,并提供相關證據,一經查實,將立刻刪除涉嫌侵權內容。